1. Introduction
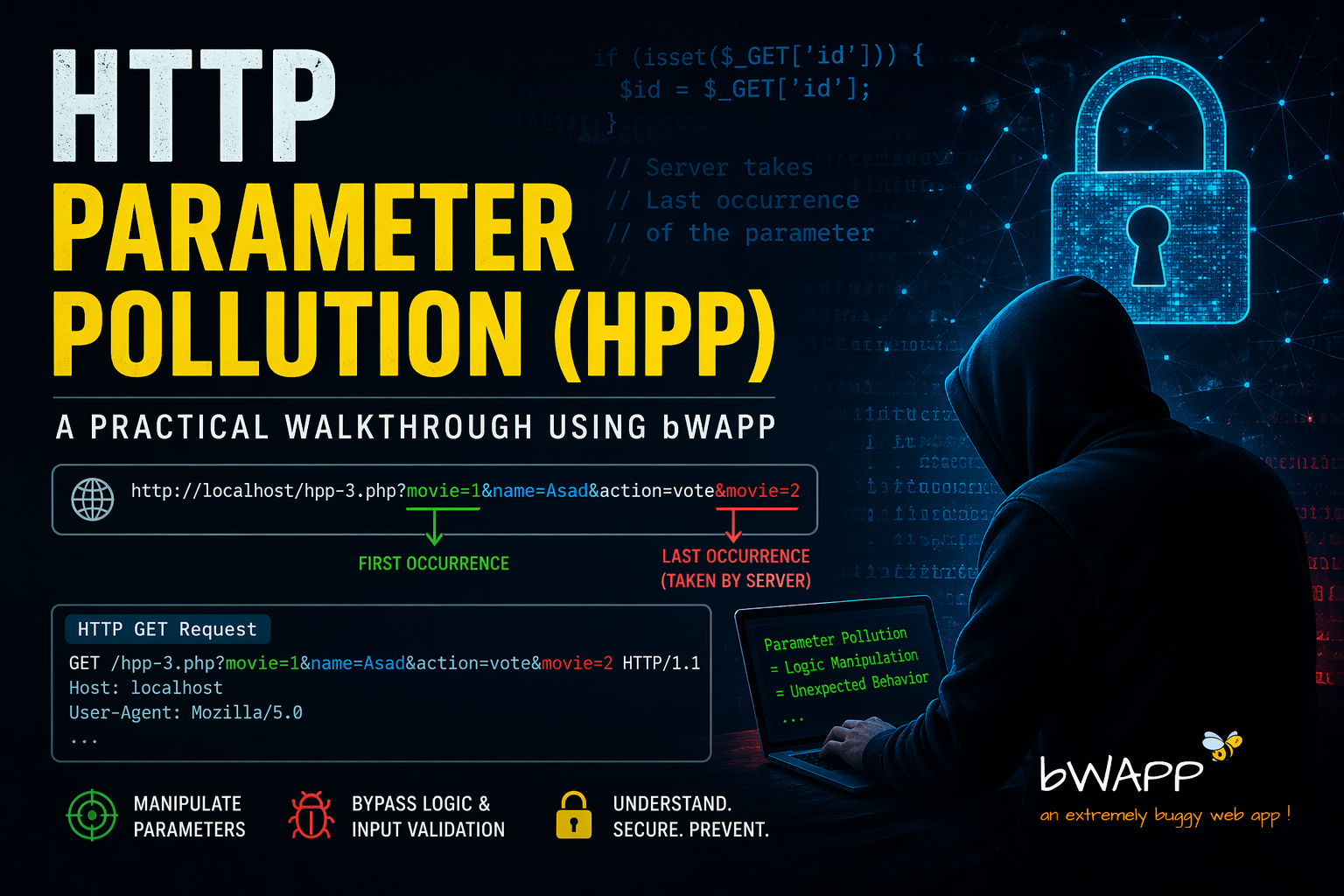
HTTP Parameter Pollution (HPP) is a web vulnerability where an attacker sends the same parameter multiple times in a request. This can confuse the application because it may not handle duplicate parameters properly. As a result, the application may behave in an unexpected way, which an attacker can use to bypass security controls or manipulate functionality.
2. What is HTTP Parameter Pollution (HPP)?
HTTP Parameter Pollution (HPP) is a vulnerability that occurs when a web application accepts multiple parameters with the same name in a single request but does not handle them properly.
For example, a normal request looks like this:
id=1
But in HPP, an attacker sends:
id=1&id=2
Now the problem is that different parts of the application may process this request differently.
- Some may take the first value (1)
- Some may take the last value (2)
- Some may combine both
This inconsistency can lead to unexpected behavior and can be used to bypass security checks.
Expected Behavior by Application Server
The following table illustrates how different web technologies behave in presence of multiple occurrences of the same HTTP parameter.
Given the URL and querystring: https://example.com/?color=red&color=blue
| Web Application Server Backend | Parsing Result | Example |
|---|---|---|
| ASP.NET / IIS | All occurrences concatenated with a comma | color=red,blue |
| ASP / IIS | All occurrences concatenated with a comma | color=red,blue |
| .NET Core 3.1 / Kestrel | All occurrences concatenated with a comma | color=red,blue |
| .NET 5 / Kestrel | All occurrences concatenated with a comma | color=red,blue |
| PHP / Apache | Last occurrence only | color=blue |
| PHP / Zeus | Last occurrence only | color=blue |
| JSP, Servlet / Apache Tomcat | First occurrence only | color=red |
| JSP, Servlet / Oracle Application Server 10g | First occurrence only | color=red |
| JSP, Servlet / Jetty | First occurrence only | color=red |
| IBM Lotus Domino | Last occurrence only | color=blue |
| IBM HTTP Server | First occurrence only | color=red |
| Node.js / express | First occurrence only | color=red |
| mod_perl, libapreq2 / Apache | First occurrence only | color=red |
| Perl CGI / Apache | First occurrence only | color=red |
| mod_wsgi (Python) / Apache | First occurrence only | color=red |
| Python / Zope | All occurrences in List data type | color=[‘red’,’blue’] |
(Source: Appsec EU 2009 Carettoni & Paola)
Walkthrough
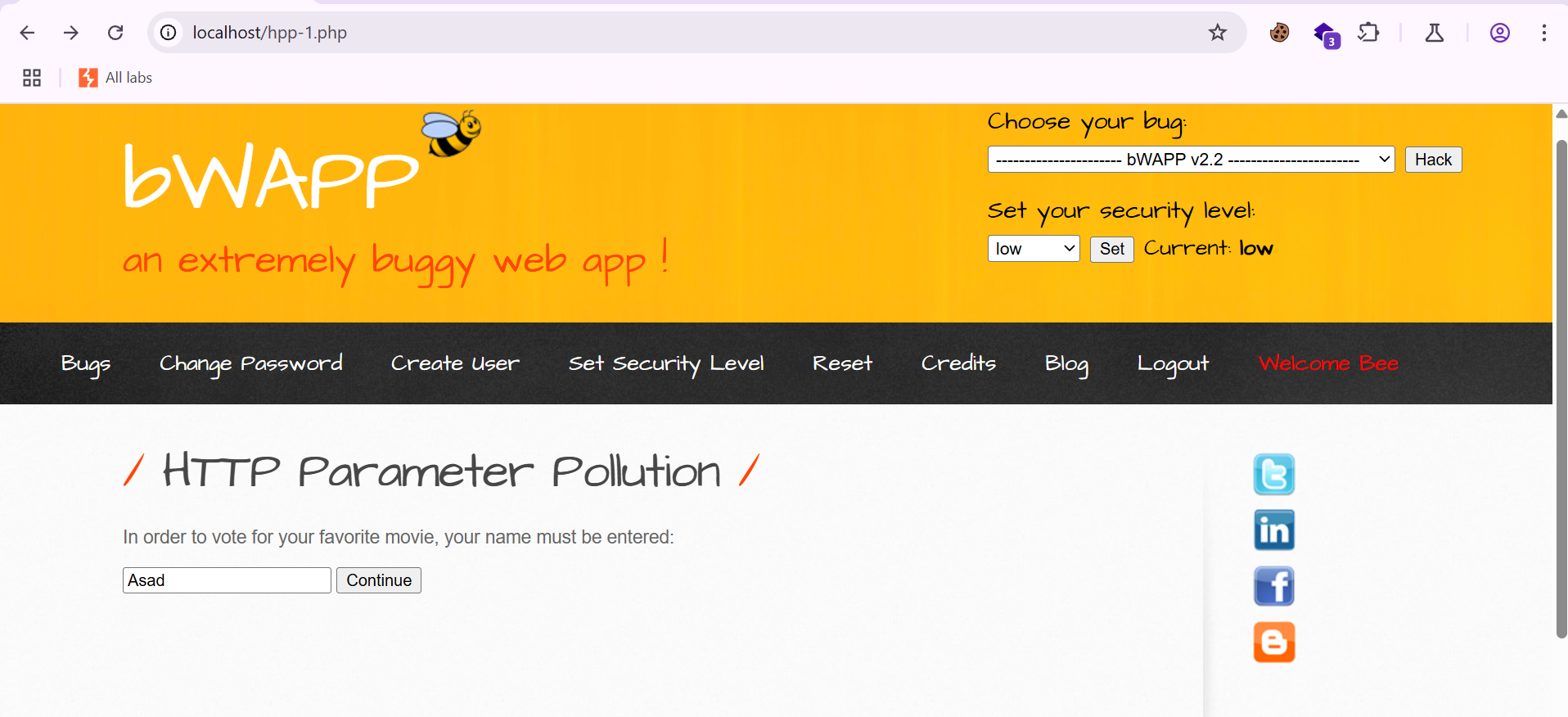
Step 1: Enter a name in the input field and proceed by submitting the request.
Step 2: We can observe multiple parameters in the URL. Now, proceed by submitting the vote.
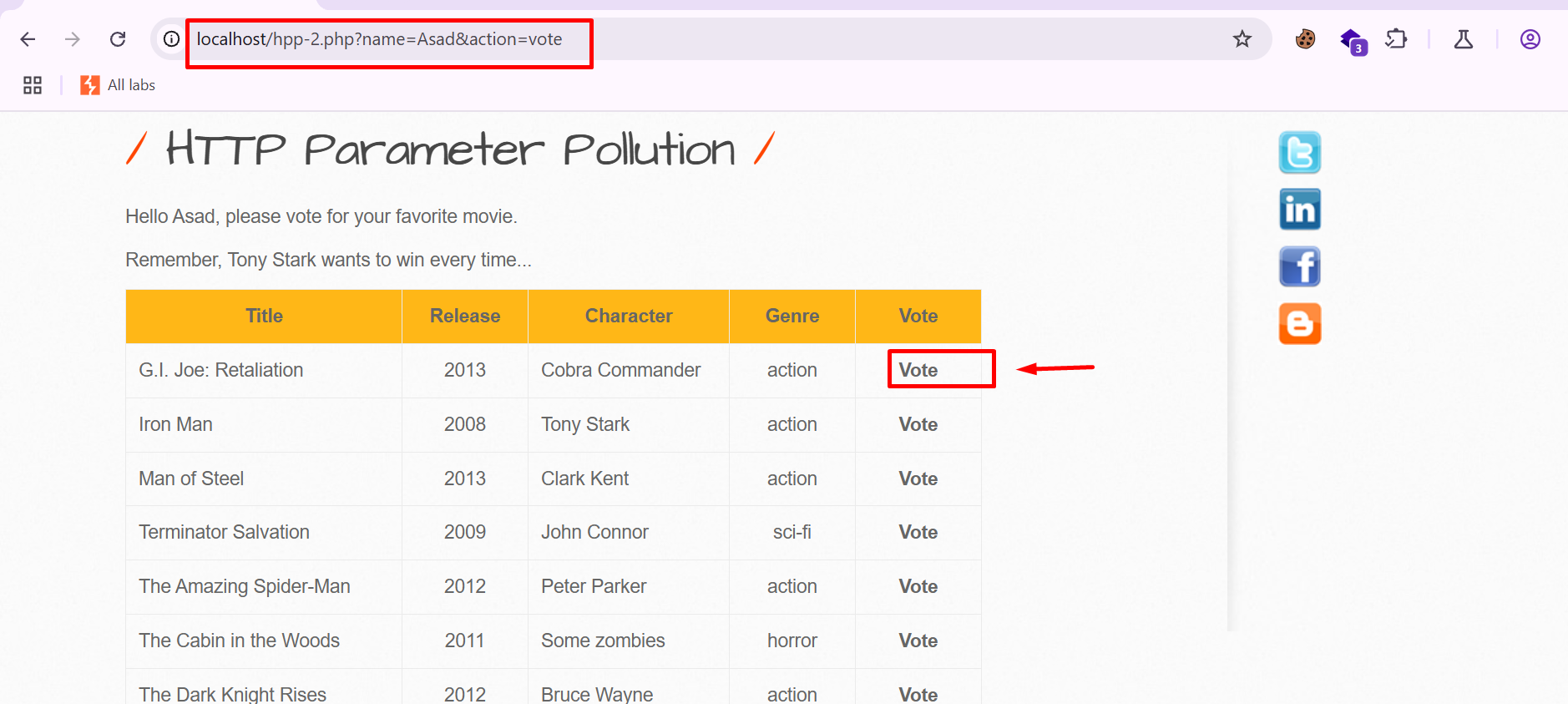
Step 3: Submit the vote for movie list number 1. As shown in the response, the vote is successfully recorded for the selected option.
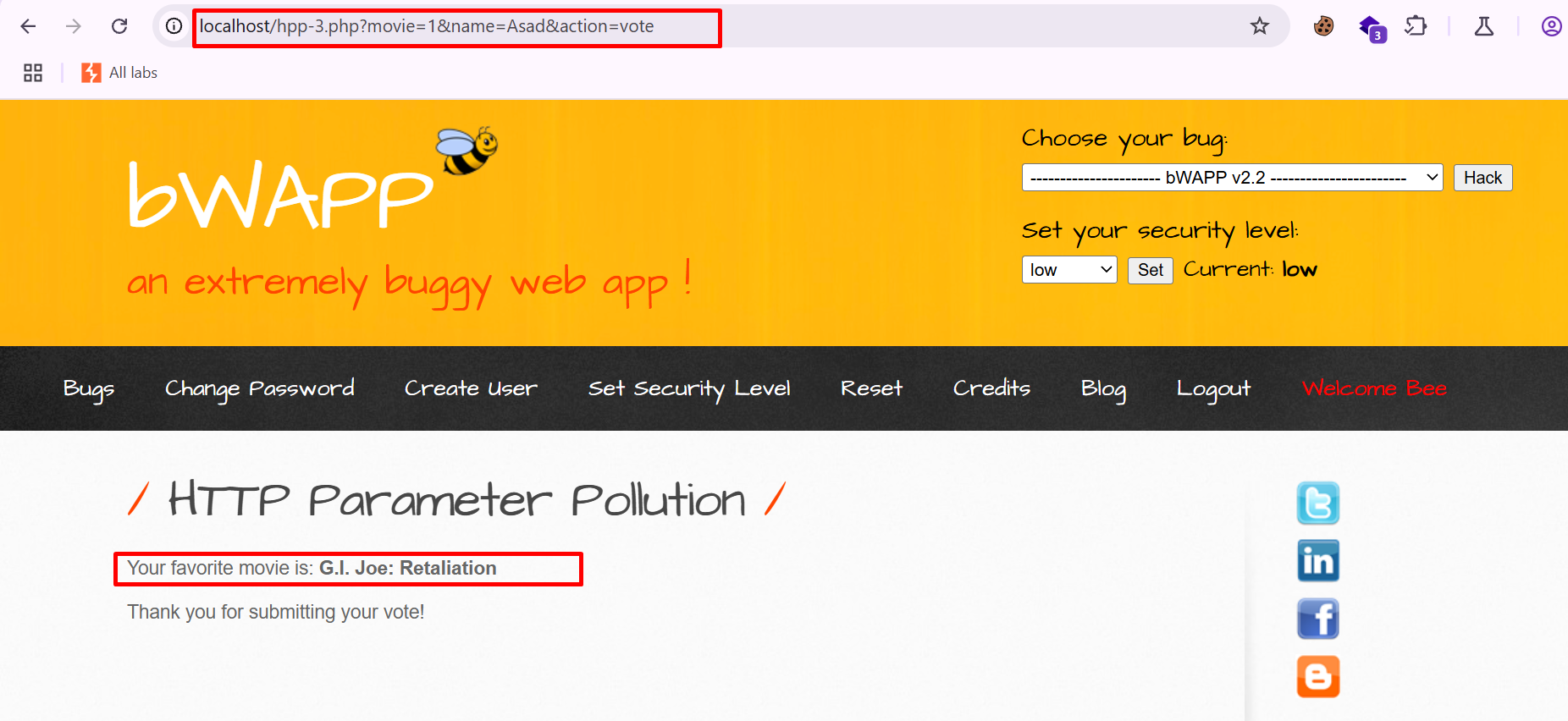
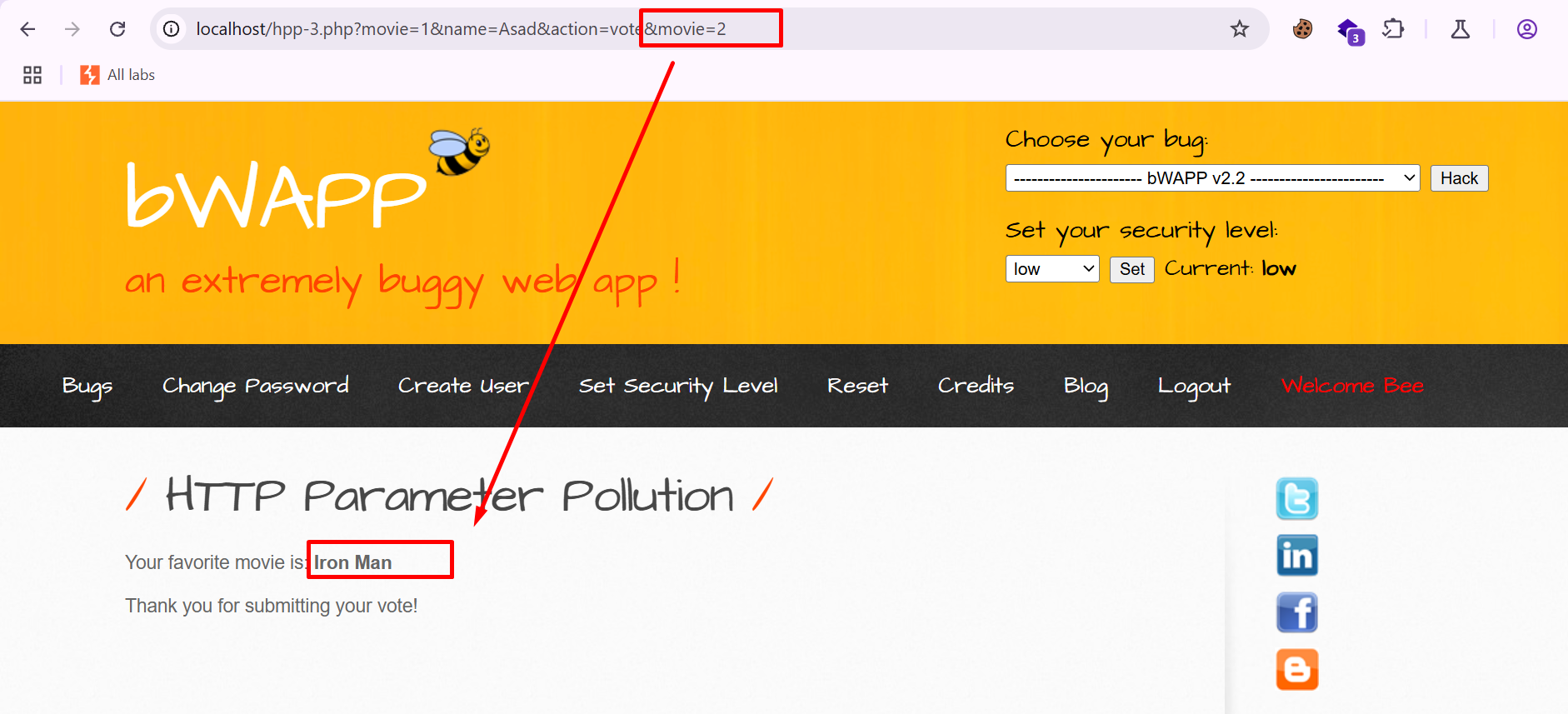
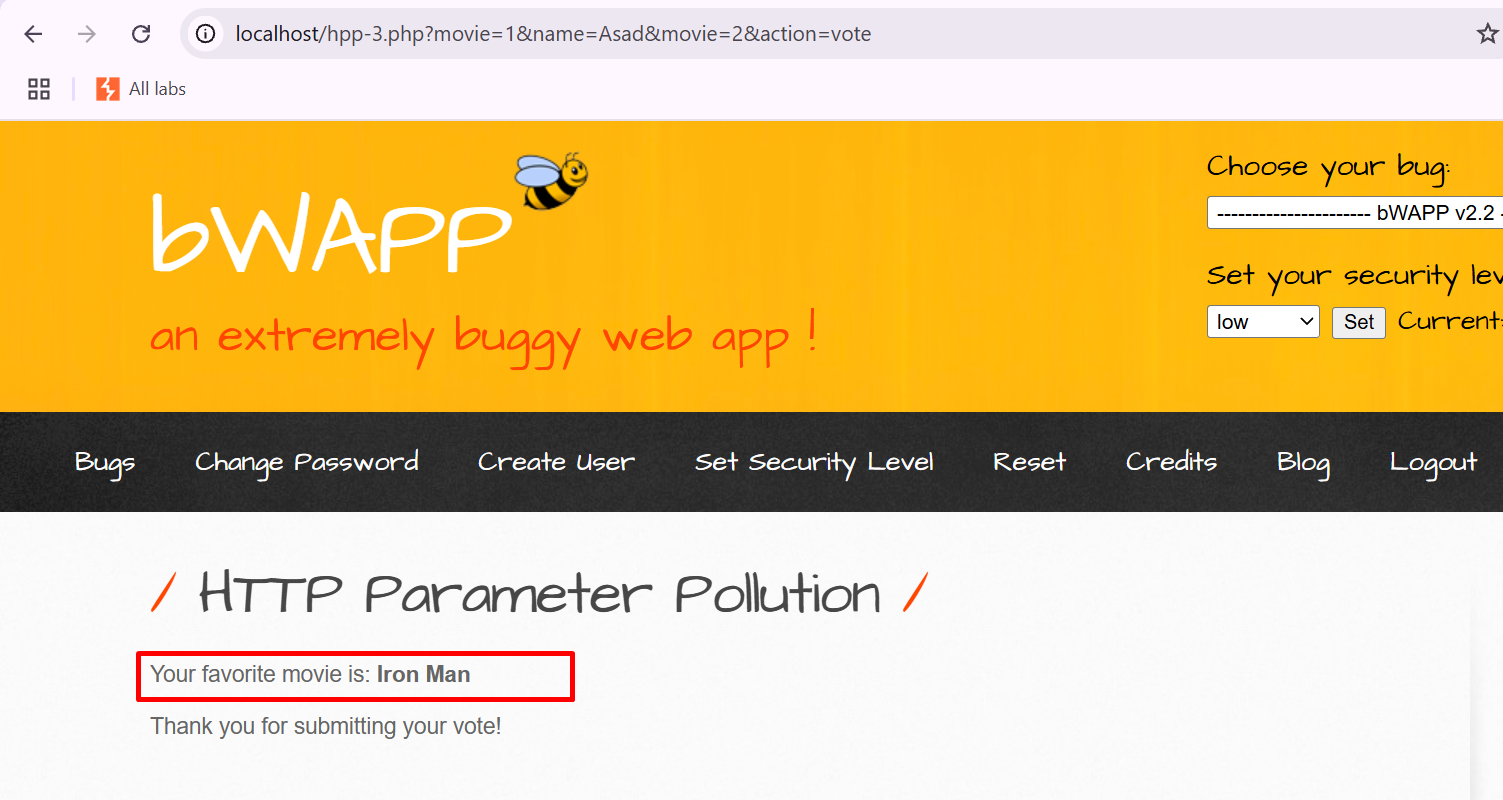
Step 4: Add an additional parameter &movie=2 to the request, which changes the vote from G.I. Joe: Retaliation to Iron Man.
URL:
<http://localhost/hpp-3.php?movie=1&name=Asad&action=vote&movie=2>
This behavior confirms that the server processes the last occurrence of the parameter.
Step 5: Register again, but this time modify the input by entering Asad&movie=2 as the name parameter to manipulate the request. Then proceed and observe how the application processes this modified input.
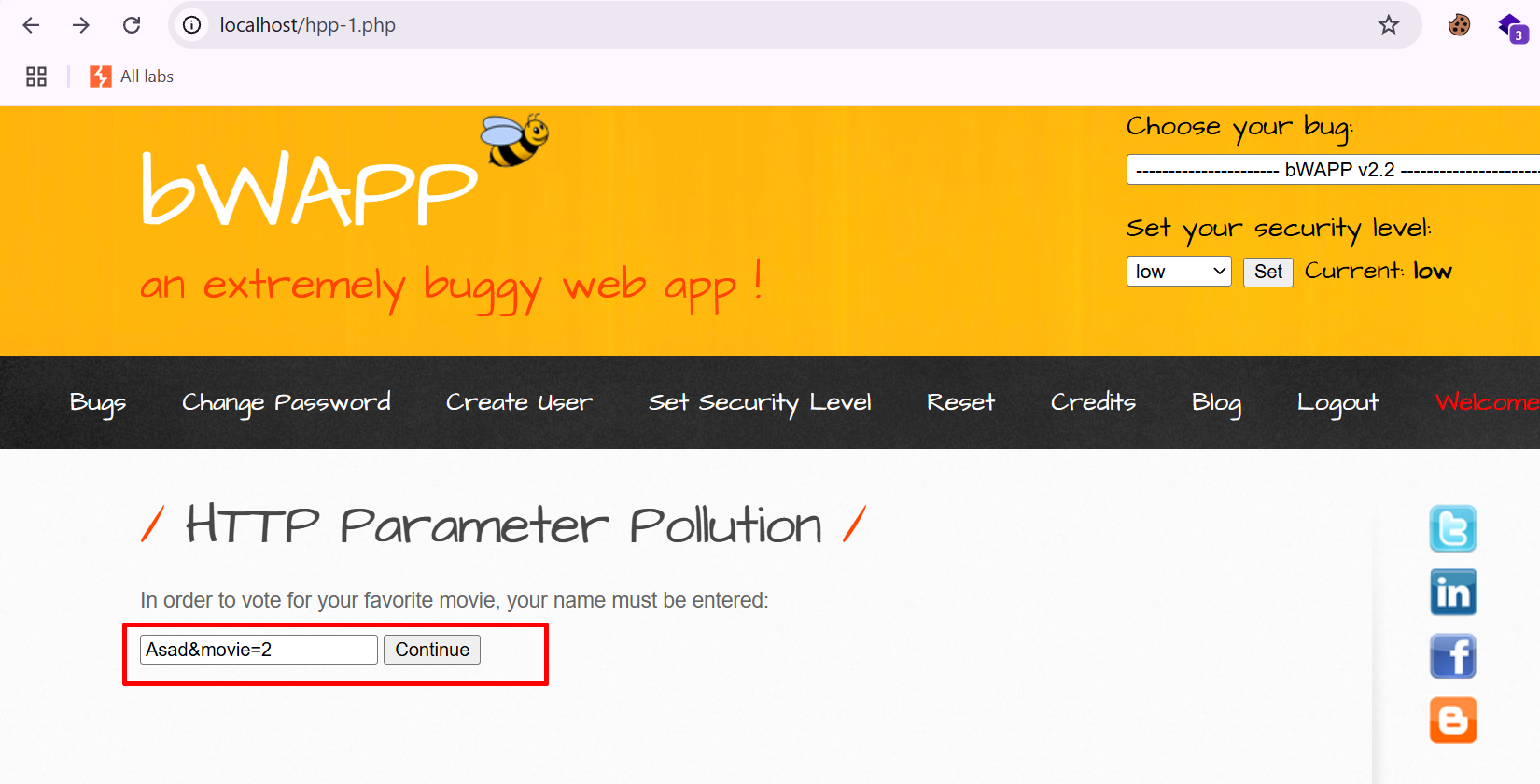
Step 6: Observe that the entered name appears in both the URL and the request body, confirming that the input is reflected in multiple parts of the request.
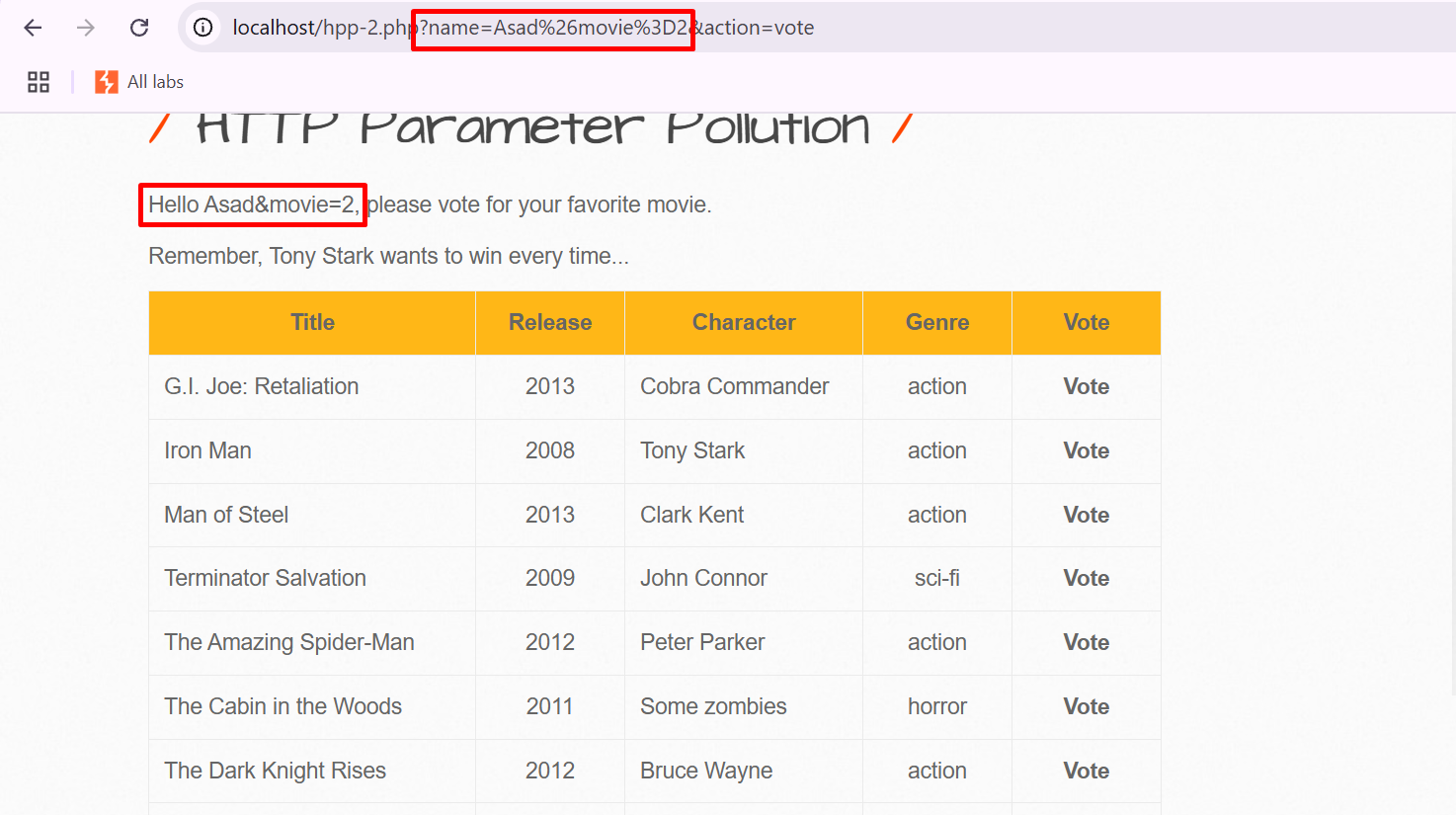
Step 7: Now, proceed to vote again for the first movie in the list.
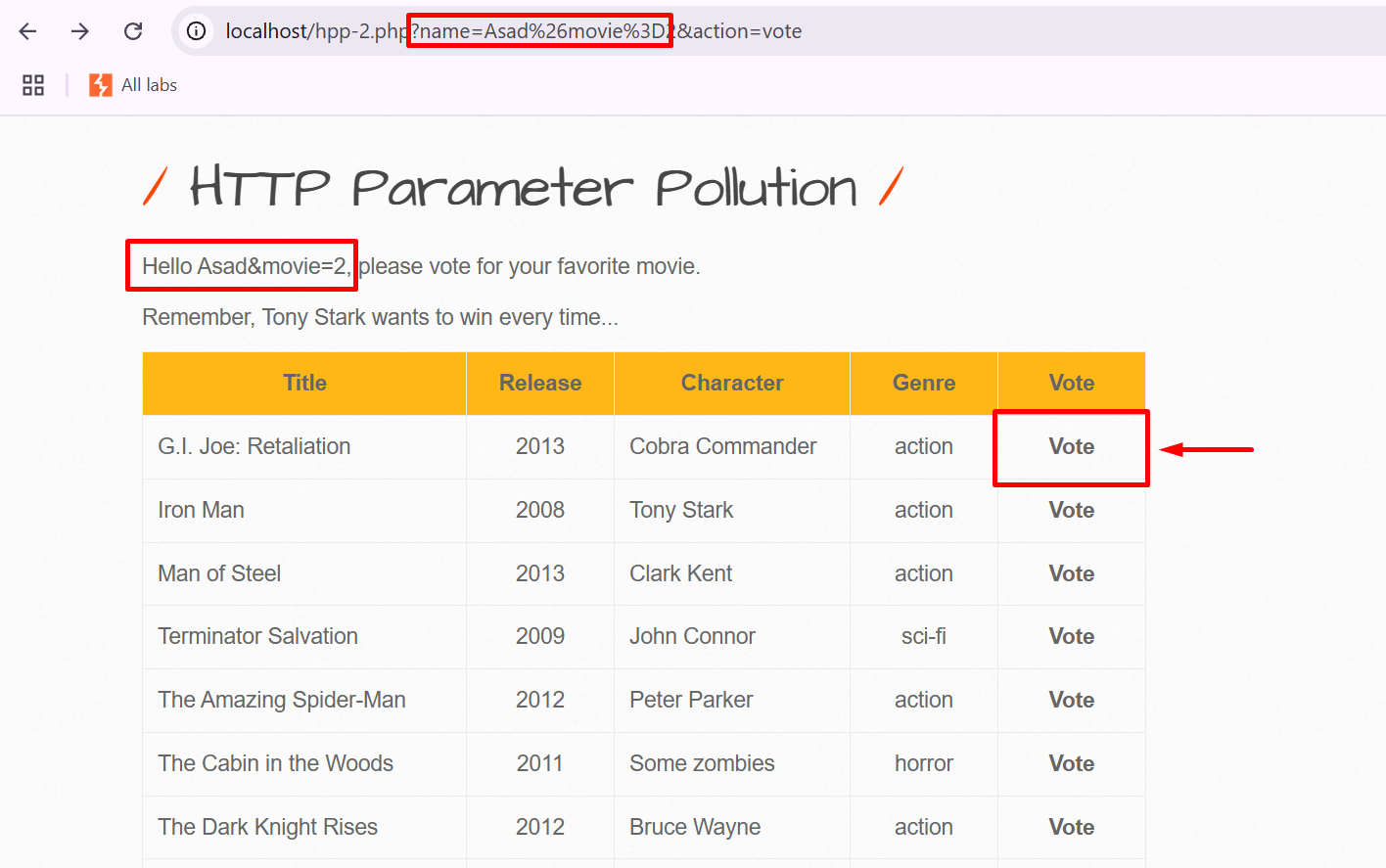
Step 8: It can be observed that although the vote was submitted for the first movie, it was processed for the second movie (Iron Man). This demonstrates that the parameter manipulation overrides the intended input, causing the vote to be redirected to a different option.
Mitigation
To prevent HTTP Parameter Pollution, the application should implement strict input validation and reject any requests that contain duplicate parameters. It is important to ensure that parameters are handled consistently across all components of the application. Additionally, developers should define a clear rule for parameter processing (such as accepting only a single value) to avoid ambiguity and unexpected behavior.


Great Information shared by you bro, It really very good insighfull.
Thanks Bro
Good Knowledge share by you.
Thanks Bro
Excellent and good knowledge thanks for the information
Thanks Bro